Credit unions and other entities who have yet to adopt Current Expected Credit Loss (CECL) need to consider how to handle the allowance modeling. One of the earliest and most critical decisions in your CECL compliance journey, the basic choice is simple: will you create your own CECL model, or will you use a vendor model?
CECL allows entities to use judgment in determining the relevant information and estimation methods best suited for their portfolios to more accurately estimate expected credit losses. CECL is not prescriptive; an entity can use a different approach for each of its portfolios.
Because it will have significant downstream impacts on CECL implementation and continued compliance activities such as data needs and the analysis of results, this modeling decision must be considered carefully.
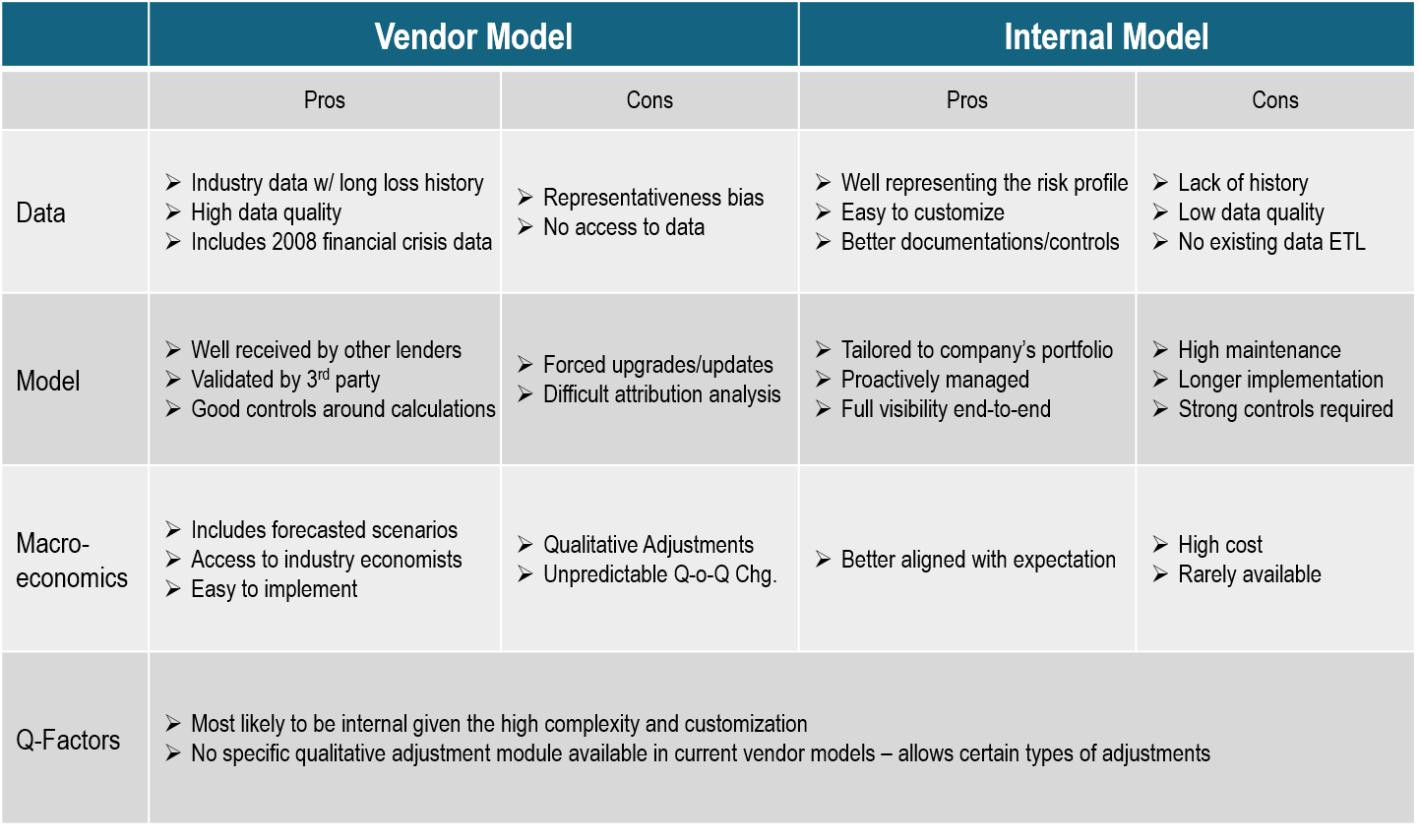
Model Consideration Matrix
As shown below, strengths and weaknesses of both the vendor and internal models reveal the many complexities of CECL. This graphic will help you to assess what type of model is right for your organization.
Make the Decision Now
The in-house versus third-party modeling decision is critical and needs to be addressed now. CECL modeling is complex, so staying in-house may require one or more of the following:
- Significant process redesign
- Documentation and controls work
- Internal resources with the right skill set to ensure that the end result readily supports CECL compliance
Choosing to employ a third-party model may be safer and more mainstream, but will require a selection process that could take more time than anticipated. It is time to get started!