For many, June 30 represents the end of the second fiscal quarter (also often referred to as “Filer Status Day”), marking the date by which companies re-evaluate their SEC filing status by determining their public float (i.e., aggregate worldwide market value of the voting and non-voting common equity held by the issuer’s non-affiliates). Whether this means exiting Emerging Growth Company (EGC) status or becoming a non-accelerated filer, a change in filing status may have a significant impact on a company’s effort to comply with Section 404 of Sarbanes-Oxley (SOX) – more specifically, section 404(b).
The move from management’s assessment of internal controls over financial reporting (ICFR) under 404(a) to the auditor’s assessment under 404(b) can come with many challenges. Where the significant change is felt most is in the level of evidence required to be documented and retained by management for auditors to attest to the effectiveness of the control environment, as opposed to management simply relying on their level of familiarity with it.
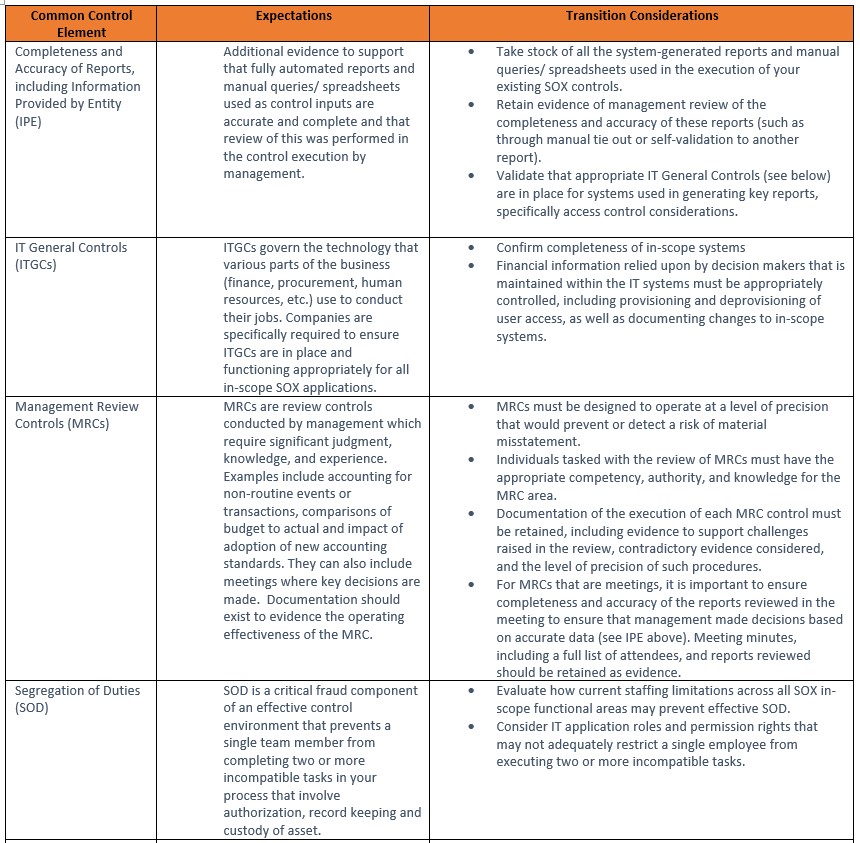
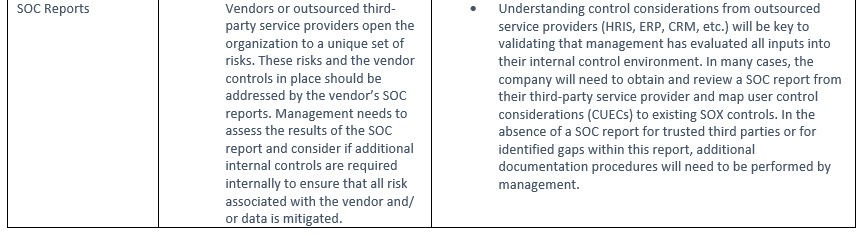
Understanding some of the challenges that are involved with this shift in filing status can help companies better prepare for a successful future as a SOX 404(b) entity. This table provides some specific examples of transition considerations for common control elements that are required under both sections 404(a) and 404(b).
As companies look to life post-Emerging Growth status or after becoming a non-accelerated filer, it is important to prepare for the demands that come with achieving SOX 404(b) compliance as early as possible. Understanding the pitfalls that may lie along the journey could help a company avoid a potential material weakness.